1. Network Architecture Study
Using a top-of-the-line tool ARCSOM can help you map your OT environment, helping you gain true insight into what assets are communicating and how!
Find unknown assets, see live traffic as it comes in, develop an understanding of what protocols are being used & who is talking to who.
Our tool uses a purely passive scanning approach to minimise all risk to the availability of your legacy PLC equipment.
Available in snapshot format or permanent monitoring setups.


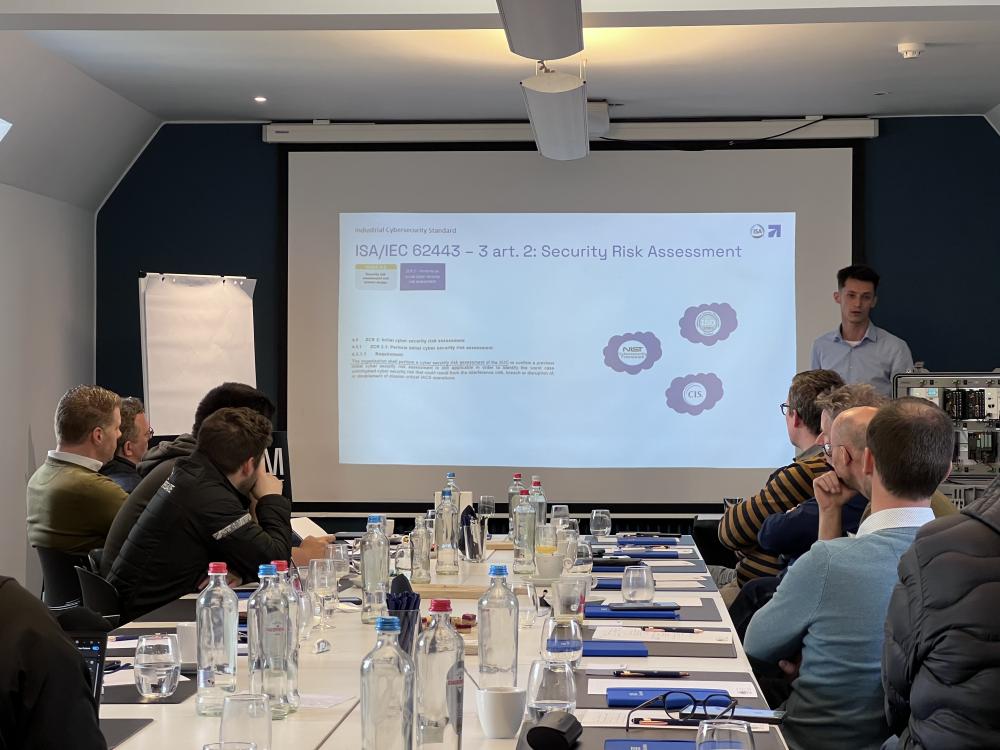
2. Risk Assessments
Due to the implementation of the NIS-2 law in Belgium, risk assessments are now a required step in achieving compliance.
As certified ISA/IEC 62443 expert, Arcsom offers a regulated and industry recognised risk analysis solution! We work through several steps like discovering system architectures, GAP-assessment, segmentation, ... to help provide you with key insights about your current OT cybersecurity posture!
Risk Analysis in a stepwise manner
1. High Level Risk Assessment
A high level approach to the assessment where we identify top threats and their respective importance to handle.
2. Zones & Conduits
We group your assets according to best practices, ensuring a good segmentation where threats can't expand horizontally or vertically.
3. Detailed Risk Assessment
We identify a set of additional countermeasures per risk and per zone.
4. Solution Proposition
We develop a custom made solution roadmap, indicating what risks to tackle first, all based on the outcome of your risk assessments.
3. Implementation
Industrial Firewalls
With the network being the #1 attack vector for most cyberattacks in OT-environments. Using proper Industrial firewalls for segmentation is key! Not only does it allow for visibility into the system's intercommunications, it also gives you a platform for hair-fine control over flows, protocols & much more.
Permanent Monitoring
As a proud partner of Seclab, We can also implement their permanent monitoring software in your OT Networks! If we have a backup of the Network Architecture Study files, we can reinstall them immediately for swift integration of the permanent monitoring setup.
Safe Configuration
Every new automation project comes with the option of explicit cybersecurity configuration & documentation. Combining our 20 years of knowledge and experience in automation systems & a deep understanding of network safety, we deliver a complete cybersecurity report of our installations, so you can directly show proof of commitment to authorities!
4
4. Industrial Security Awareness & Trainings
NIS-2 Compliancy is Required by law and not as straight forward as we all would have hoped. Thankfully Arcsom's certified OT Cybersecurity experts can help guide you towards compliancy!
Arcsom offers comprehensive expositions where we teach you the in's & out's of NIS-2, ISA 62443 and general OT cybersecurity best practices. Thanks to our many years of expertise, we can help you weave a path through the maze of regulations!
Want to know more about the Impact of EU laws like NIS2 & CRA on your production site? Let our expert

teach you all about it!
OT Cybersecurity Project? Talk to an Arcsom expert today!

Jarne
OT Cybersecurity Manager






